What is an extranet, and how can I use it?
Good communication sets the foundation for effective teamwork. This applies to communication within companies, as well as to communication with people outside of the company. Regardless of whether an exchange concerns orders from a supplier, production instructions for selected customers, or clarifying details by phone or e-mail - it all takes time. An extranet provides an opportunity to give information to a selected group of people. But what is an extranet exactly? How does it work, and for what purpose can you use it?
Extranet: definition and distinctions
The word extranet is composed of the Latin "extra" (outside) and the English “net”. It refers to a controlled private computer network that uses the internet to connect a specified group of external users and give them access to a computer network. An extranet serves to provide resources that are made available to the authorized users, but not to the public. Possible external users are business partners, suppliers, and selected customers. By setting up an extranet, it’s possible to simplify the exchange of information across company boundaries – this applies in particular to communication between the company's own employees and external parties.
Differentiation to other computer networks
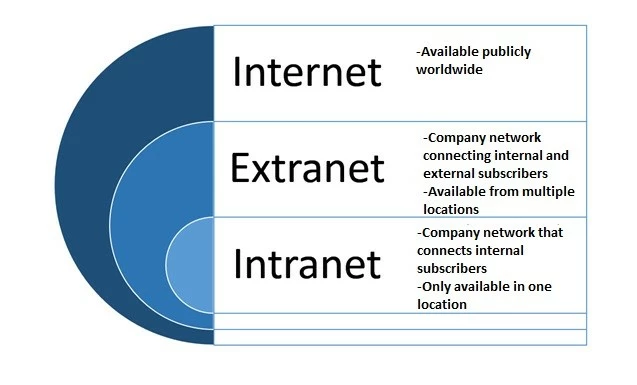
An extranet is an extension of an intranet which uses the same techniques as the internet. A comparison in a company setting illustrates the differences:
- Intranet: an intranet is a company network that connects internal participants with each other and thus facilitates the exchange within the company. It’s usually only available at one location. Access rights for individual participants are regulated by access controls, groups, and user roles. This means that not all users of the intranet have access to all areas of the company. Restrictions on access rights can be used, for example, to make information available only to individual departments.
- Extranet: An enterprise network that connects internal and external subscribers via subnetworks, facilitating exchanges between employees and people outside the company. Access to the extranet is possible from several locations. External users are not granted access to the entire intranet, only certain areas are made available to them. In the extranet, access controls as well as groups and user roles regulate which information participants can access – suppliers and customers have different access rights, for example.
- Internet: The internet is a publicly available worldwide network. It’s not a homogeneous network, but consists of many subnetworks.
How can you use an extranet?
Whether for private companies, universities, or associations – by setting up an extranet, you create a comprehensive information network that can be integrated into business processes in various ways:
- Data transmission: An extranet enables electronic data exchange (or "EDI") of documents such as order forms or delivery notes between business partners. In this way, data can be exchanged across company boundaries and processed directly without manual entry. This means that data transfer can be carried out independently of merchandise management systems.
- Data maintenance: Data can be updated and made available to authorized users within a short period of time. This ensures a high degree of topicality and transparency in data processing.
- Cooperation: An extranet enables the joint use of software applications and cooperation with other companies.
- Transmission of information: News that is of interest to a selected group of people can be made available to them within a short time.
- Knowledge management: Sharing of training programs or joint development of certain applications in cooperation with other companies.
Companies can also integrate additional functions into the extranet to facilitate the exchange with external parties. Possible functions would be a search engine, a personnel directory, or a messenger service. Interactive functions (such as conducting surveys and votes) are also possible.
How does an extranet work?
Technically speaking, the extranet is structured like the internet. Communication takes place via a collection of about 500 network protocols, which work according to which rules and in which format communication takes place. The internet protocol (IP) and the transmission control protocol (TCP) form the basis for data exchange.
How is an extranet secured?
Security precautions are very important when handling private data. It’s not only necessary to make sure that unauthorized persons outside the company don’t access confidential information, but also to close security gaps within a company. To secure the extranet and protect confidential data from unauthorized access, two main security measures are used:
- Firewalls: A firewall prevents unauthorized persons outside a company from accessing data on the extranet.
- Passwords: Passwords prevent unauthorized persons (also within a company) from having direct access to data stored on the server.
An effective protection of the extranet is guaranteed by an external firewall. It’s set up between different computer systems and is therefore also known as a network or hardware firewall. Unlike the personal firewall, it does not run on the protected system itself, so it’s difficult to manipulate.
So-called demilitarized zones (DMZs) are often used for protection. They serve as a buffer zone between the private company network and the internet, separating the two networks by strict access rules. DMZ is most effective with two firewalls. An external firewall isolates the DMZ from the public network, an internal firewall isolates the DMZ from the intranet.
You can also guarantee the most secure access to data via so-called virtual private networks (VPN). A VPN is a private communications network where the subscribers are connected via a virtual IP tunnel, and can access the company's internal intranet through the tunnel. To ensure a high level of data security when using public lines, all information is transmitted in encrypted form (tunneling). This means that the transmitted data is not visible to other users on the public network.
How to create your own extranet
There are essentially two different approaches to creating an extranet and integrating it into corporate communication. Both approaches are portal solutions:
- Enterprise portals: These combine different applications under a single user interface. This is particularly advantageous if many different extranet applications are to be integrated. In this way, users don’t have to deal with different operating concepts. In addition, identification is only carried out once in relation to the portal, not for each individual application.
- Process-oriented portals: These primarily serve to handle certain business processes. Possible examples are orders or travel expense accounting. The individual business processes can be integrated into the portal, but don’t have to be. They can also be implemented via separate applications.
An extranet can also be set up on the foundation of a content management system (CMS). The range of functions covered by the standard software varies depending on the system used. If the required functions are not covered by the standard software, it’s often possible to supplement them with extensions. However, you should keep in mind that implementing and maintaining complex systems requires a certain amount of expertise.
If you are unsure which solution is right for you, it’s advisable to consult an expert.
Pros and cons of using an extranet
What are the advantages of an extranet?
The implementation of an extranet has many advantages for companies. This includes the rapid exchange of data between internal and external employees as well as external staff. Since large amounts of data can be exchanged quickly via an extranet, many processes can be optimized. Reduced time spent on manually executed applications often results in increased productivity and cost savings. Order status information, for example, no longer has to be sent to each individual customer by e-mail. The corresponding customer simply accesses the current order status via the extranet. Since the extranet eliminates the need for separate EDI software, additional costs can be saved, and finally, because fewer manual processes have to be carried out, there are fewer possible sources of error.
What are the possible cons of having an extranet?
The advantages of an extranet are also faced with some disadvantages. This includes, for example, the acquisition costs of the corresponding software. In addition to the initial costs associated with the production, there are also consequential costs. For the extranet to fulfil its purpose, it must be regularly maintained by internal employees or an external service provider, for things such as software updates, backups, and problem solving. In addition, the required training time for employees results in correspondingly high opportunity costs, especially for systems with complex applications. In other words, during the training period, employees don’t have time to perform their actual tasks, which may reduce a company’s turnover, especially when many employees need to be trained at the same time.
In addition to the costs, possible security risks must also be taken into account. High security standards must be maintained to prevent unauthorized access to sensitive data. This applies to access from outside as well as unauthorized access within the company.
An overview of the pros and cons
| Pros | Cons |
|---|---|
| ✓ Fast data exchange | ✗ Acquisition and follow-up costs |
| ✓ Increased productivity | ✗ Employee training needed |
| ✓ Time and overall cost savings | ✗ Increased security risks |
| ✓ Easy to keep up to date | |
| ✓ Optimized communicated with external parties | |
| ✓ Improved information management |