How to sign emails digitally
Sending an email with a fake address is no big feat for skilled internet fraudsters. That’s because many companies fail to install additional security measures when emailing invoices or sensitive documents to customers or clients, potentially opening the door for criminal activity. Phishing, a technique that has become increasingly widespread in the past few years, is a particularly dangerous form of fraudulent e-mailing. Fraudsters send e-mails in the name of companies or other seemingly trustworthy senders, with the hope of obtaining access to personal or payment information of their unsuspecting recipients.
A reliable security solution to verify trustworthy senders is the use of digital signatures. When an email includes an electronic signature, the recipient can rest assured that its content has not been tampered with and the sender is indeed who they claim to be.
What is a digital signature?
An electronic signature guarantees the integrity of both the data and the sender of an e-mail. They’re used to digitally authenticate the origin of digital information – not just e-mails, but documents, too. In this way, a digital signature fulfils a similar role to a physical signature, and it ensures the authenticity of the person or company listed as the sender of electronic information.
By using a digital signature, you can protect the integrity of any data you transfer online. The recipient can be certain that nobody has accessed or tampered with the content because the electronic signature acts as a seal. This means that in cases of dispute, this signature can be used to prove exactly where an e-mail came from. Both the person (or company) who signed the email, and the content of the e-mail are on display for the recipient to see.
Digital signature vs. email signature
A digital signature should not be confused with the classic, stylish signature that you can create and include in any e-mail. Despite the similar name, the latter refers to a text-based signature at the bottom of an e-mail that appears in a similar form to a hand-drawn signature and usually precedes contact information of the sender, like a name, an address, a telephone number, and a job title. Instead, a digital signature is a general electronic signature, typically comprised of three algorithms:
- A key generation algorithm (responsible for selecting a random private key and corresponding public key)
- A signing algorithm (produces the signature when presented with the message and the private key)
- A signature verifying algorithm (responsible for accepting or rejecting authenticity claims)
Generally, a digital signatures is referred to as a cryptographic signature that can be verified by the recipient and ensures that an email has not been tampered with. In comparison to encryption, message signing uses the sender’s private key to sign and to read the signature. Encryption, on the other hand, converts plain text into cipher text which is a non-readable format.
 To display this video, third-party cookies are required. You can access and change your cookie settings here.
To display this video, third-party cookies are required. You can access and change your cookie settings here. Function: how to create a digital signature
If you’re looking to digitally sign your e-mails, there are two standard practices available: S/MIME and OpenPGP. Both work on the same basic principle, but they use different data formats; the majority of software solutions only support one of these two formats.
Competing systems, additional effort, and sometimes high costs are often cited as the main reasons for the low distribution of signed emails.
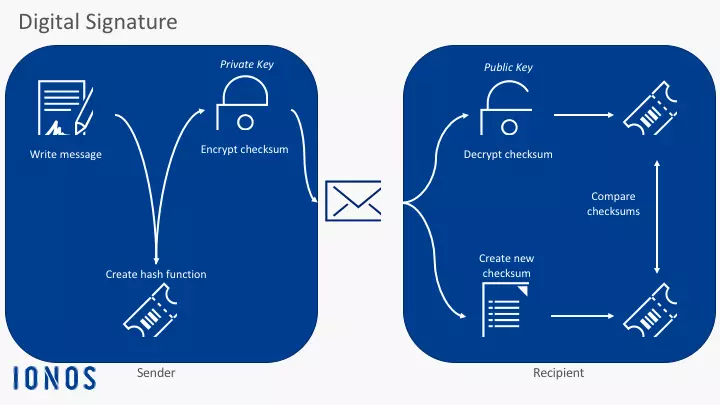
The basic principle when it comes to creating a digital signature is the concept of asymmetric encryption. This means that the sender receives two keys from the key generation algorithm: a private key and a public key. The mail program of the sender automatically creates a checksum of the mail content, using a hash function which is encrypted using a secret key and attached to the email.The public key is either sent with an attachment or obtained by the recipient via a public directory. The mail program of the receiver then decrypts the checksum, recalculates it and then checks the results. If the results match, you can be sure that the message has been signed with the private key that matches the corresponding public key. The authentication is successful and the e-mail is proven to have come from a trustworthy source and to have arrived without manipulation.
- Write perfect emails with optional AI features
- Add credibility to your brand
- Includes domain, spam filter and email forwarding
One requirement for the use of digital signatures is that your e-mail client is configured correctly in advance. If that’s the case, the process described above will take place automatically in the background, without you noticing. For information on how to set up your e-mail client for this, check out the support page for the software you’re using, for example Microsoft Outlook or Mozilla Thunderbird.
How do you assign a public key to a sender?
Needless to say, this procedure would only make sense if the recipient can identify the sender beyond any reasonable doubt. So the official certification authority (CA) only provides the key after first identifying the sender; only once the certification authority has issued a certificate can the key be officially validated. Since the recipient’s system has to recognize the key in order to ensure the authenticity of the certificate, this information also has to be downloaded and installed by the certification authority. The e-mail program then later picks up the authentication automatically.
Trust levels of certificates
The pair of keys that is used to sign an e-mail digitally has to be verified by the certification authority. This authority checks and confirms the identity of the applicant making the request. There are different levels of quality assurance certificates. Depending on how the identity check performs, a certificate may be awarded in either Class 1, Class 2, or Class 3.
- Certificate level Class 1: a top-level, Class 1 certificate means that the applicant simply receives an e-mail from the certificate authority that must be acknowledged.
- Certificate level Class 2: for Class 2 certificates, the applicant must submit a copy of a valid photo ID to the certification authority to prove his/her identity.
- Certificate level Class 3: this Class 3 certification is the strictest form of identification for digital signatures. It requires the applicant to be verified in person. Often this involves the applicant heading to their local post office or designated government building with an identity card to have their identity officially confirmed.
Specialist certificates: gateway or team certificate
The certificates mentioned above are usually issued for e-mail addresses for a specific sender. Theoretically, you’d need a separate certificate for every person in a company.A special exception to these certificates above is the gateway certificate, otherwise known as a domain certificate. This certificate is valid for all e-mail addresses registered under a particular e-mail domain (e.g. @example.com). The problem with this is that although the use of this gateway certificate is standardized internationally, some e-mail clients can’t process them properly. When it comes to Outlook Express, for example, neither sending nor receiving e-mails with gateway certificates is possible. Microsoft Outlook will unfortunately register the certificate as invalid upon reception and return an error message.
A team certificate can be awarded to an e-mail address that’s managed by a number of people rather than just one individual, like info@exampleg.com, or application@example.com, for example. Here there aren’t any problems during sending or receiving, because the same technical conditions are in place. The difference only occurs in the handling of the certification authority.
Requirements of a digital signature
In order to gain the access mentioned above, a signature must meet certain conditions. Most programs, including Outlook, check these conditions automatically when an e-mail with a digital signature is being sent or received, and notify the user in cases when some requirements aren’t fulfilled and so the integrity of the signature can’t be guaranteed.Since a digital signature is always associated with a certificate, it’s sensible to ensure that the certificate is current and valid. The certificate must also be issued by a trusted certifying body (certificate authority). While some e-mail programs offer their own solutions, there are a number of reliable, expert CAs that can help. Some of the best-known examples include:
Because a digital signature always works in conjunction with a certificate, it must be valid and current. The certificate also needs to have been issued by a trustworthy authority. In the US, individual states issue lists of approved cryptography certificate authorities. IdenTrust, for example, is a large provider of digital certificates for financial and healthcare businesses.
The authorities are monitored according to the US E-Sign code and the UETA to ensure that signatures are valid and take legal effect, i.e. they are enforceable.
There are also several industry organizations which address certification issues and promote relevant standards, including the Certificate Authority Security Council, the Common Computing Security Standards Forum and the CA/Browser Forum.
Digital signature vs. email encryption
Digital signatures are often used in combination with e-mail encryption, but the two do work independently of one another. Signing an email digitally means - quite literally - putting a digital mark onto an e-mail to guarantee the authenticity of the sender. This protects the e-mail from manipulation, but it can still be read by third parties on its way from sender to recipient, just like an electronic version of a postcard. Digital signatures also protect content too: your e-mail can’t be edited, but it can still be intercepted and read. Picture your electronic postcard in a clear, plastic envelope.E-mail encryption goes a step further. Sticking with the postcard example, we can imagine encryption to be sealing our electronic postcard inside an opaque envelope. The e-mail content is protected on its journey, and only the person who has the required key can decrypt the message at the other end and open the envelope to read the postcard. This makes e-mail communication trustworthy and considerably more secure. Further information on encryption and how to use it with PGP can be found in our digital guide to email encryption.