Victor MoussaShutterstock
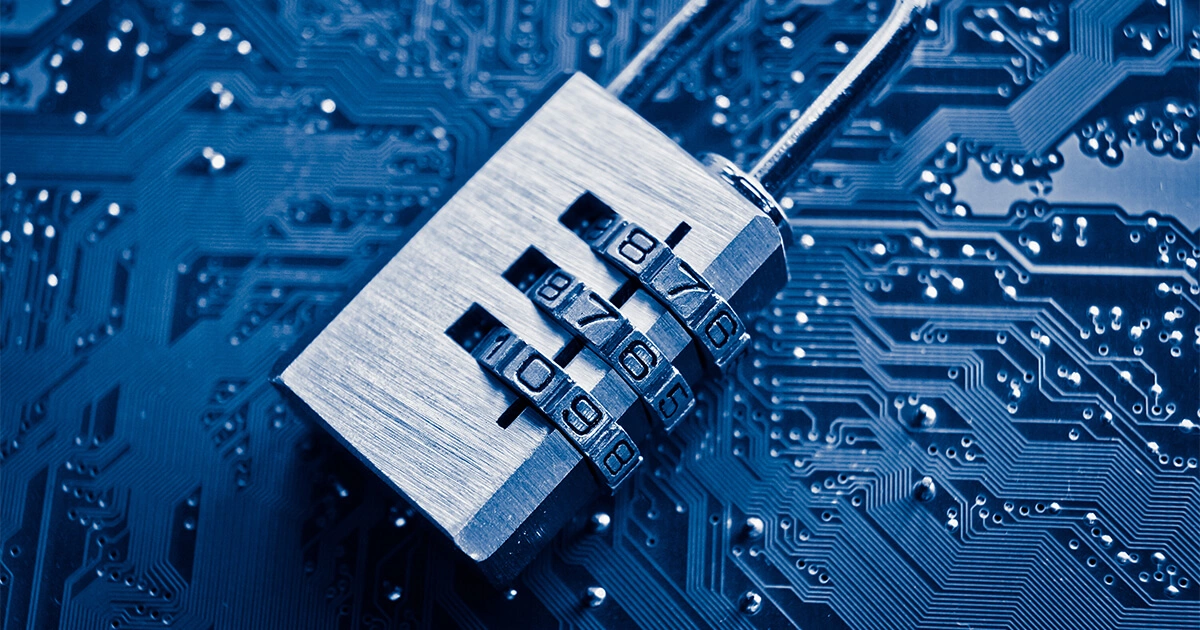
Victor MoussaShutterstockHow to encrypt and sign your emails with S/MIME
Sending an email without extra security is akin to sending a postcard: If everything goes as expected, the message arrives intact and unread by anyone else. But if the postcard or email is intercepted during transit, the content can be read or altered freely. Discover how the…