Neighbor Discovery Protocol (NDP) – what is it?
The internet protocol is an indispensable part of the internet and local networks: However, in order to ensure the transport of digital information and that the correct data packets are sent to the correct target host, a number of additional help and routing protocols are required. That is what the internet protocol family, or the internet protocol Stack are about. Dynamic Host Configuration Protocol (DHCP), for example, ensures that clients are assigned the appropriate network address during the IP connection setup. The Neighbor Discovery Protocol (NDP) helps the communication between neighboring hosts in local networks, and determines the gateway router.
Neighbor Discovery Protocol definition.
The Neighbor Discovery Protocol is used in conjunction with the newer version of the internet protocol (IPv6). Its main function is the resolution of IPv6 addresses into valid MAC addresses, the respective devices’ underlying hardware address. In IPv4, this function takes the Address Resolution Protocol (ARP). All determined addresses are stored as information in the so-called neighbor cache. This buffer not only informs network users about the local addresses of the neighboring clients, but also supplies them with additional information required for the availability check, for example. As already mentioned, the NDP is additionally involved in the allocation of the Standard Gateway. With the addition of the Router Advertisement Protocol (RA), both the standard router and the valid network prefixes – two basic parameters of the network configuration – can be determined. Finally, the network protocol, which exchanges data only within a network, also acts as a support protocol for the dynamic address configuration. This process is also known as Stateless Automatic Address Configuration (SLAAC).
How does the NDP work?
Any device that uses the Neighbor Discovery Protocol for network communications manages its’ own neighbor cache. In this, all devices of the known network are listed and can be verified by their unique device addresses (MAC). Here you can see whether the buffered address belongs to a simple client or, for example, to a router. However, the neighbor cache is not a standalone, but one of four buffers carrying out the functions of the NDP protocol. The other three components, which are also handled by each device separately, are as follows:
- Destination cache: The ‘target’ cache includes entries about all hosts on the network, which have already been sent data packets. Each of these entries, in turn, refers an address link in the neighbor cache which should be used as the next hop (intermediate station) when sending data packets to the desired destination host.
- Prefix cache: The prefix cache, or prefix list is used to manage all prefixes that apply to the network where the client resides. This listing is necessary, on the one hand, because IPv6 supports multi-homing – i.e. the accessibility of the network via two different providers – and on the other hand, allows the address space to be split into different prefixes. By using the entries in the prefix cache, NDP ensures that the target host is on the same subnet. Each prefix, except for the MAC address (also, link layer address), has a defined validity period so that the cache always remains up to date.
- Default Router List: The default router list includes all known routers that regularly contact the device. Only active routers are listed because the expiration date is automatically defined for all representatives. An extension or refresh is only possible if the router is returned.
In order to create different caches for the NDP, a different internet protocol is used, which is known as ICPMv6 (Internet Control Message Protocol for the Internet Protocol Version 6).
NDP builds on these five ICMPv6 types
ICMPv6 is commonly used in the current version of the internet protocol family as a relay for error and information messages, and it is also used by the Neighbor Discovery Protocol in the form of 5 different types of ICMPv6. Depending on the type, certain notifications are used – these help to form temporary storage or lists.
Type 134: Router Advertisement
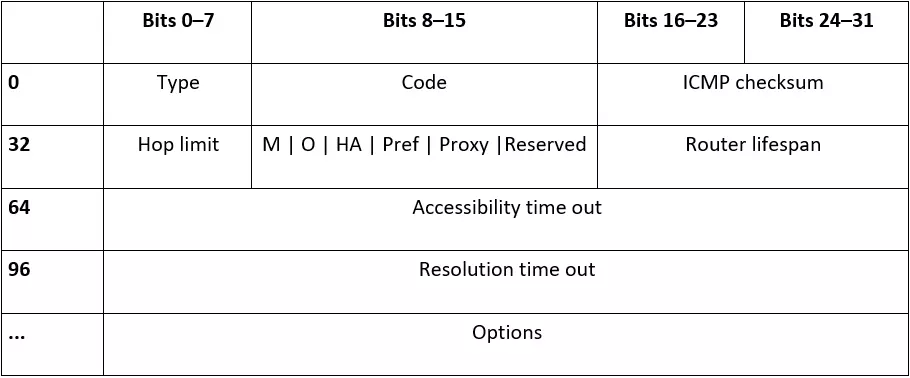
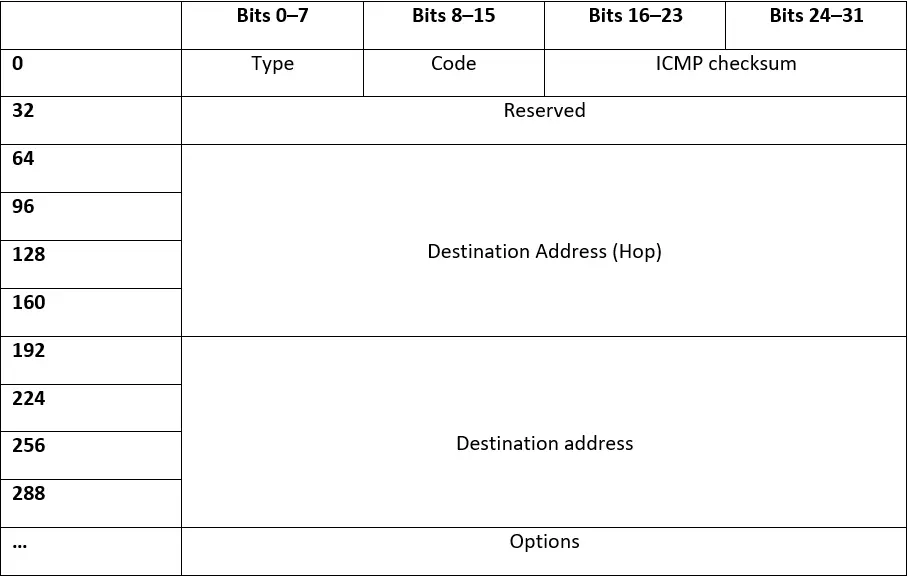
Routers periodically send out so-called router advertisements – ICMPv6 type 134 messages – to inform network members of their presence. They then distribute, among others, their routing information and the necessary parameters for automatic IP configuration. The destination of the message is usually the default multicast address range ‘ff02 :: 01', via which all hosts deemed to be valid are addressed. They also receive the routers’ address (default gateway) and the global prefix in the same way. The scheme of a routing advertisement looks as follows:
This type of message therefore has a standard length of 128 bits, with additional bits for options. Valid options include the routers’ MAC address, the ‘Maximum Transmission Unit’ and all relevant prefix information.
The ‘type’ field is set to 134 and the ‘code’ field are always set to 0. That is followed by a 16-bit ICMP checksum and an 8-bit length specification of the hop limit, which may include the stations recommended by the router.
After that follow single bits, which provide insight into:
- Whether IP addresses can be obtained via dynamic DHCPv6 (M)
- And whether other address information can be obtained via dynamic DHCPv6 (O).
The ‘reserved’ field remains unused and is ignored by the recipient. In addition, the router advertisement contains figures about:
- The time in seconds that the router should remain in the default router list (router lifespan, 16-bit integer, maximum 65535).
- The time in milliseconds that an address in the neighbor cache should still be available after reaching availability (availability time-out, 32-bit integer, maximum of approximately 50 days).
- The time in milliseconds after which a neighbor solicitation message (see below) should be resent (resolution time-out, 32-bit integer).
Type 133: Router Solicitation
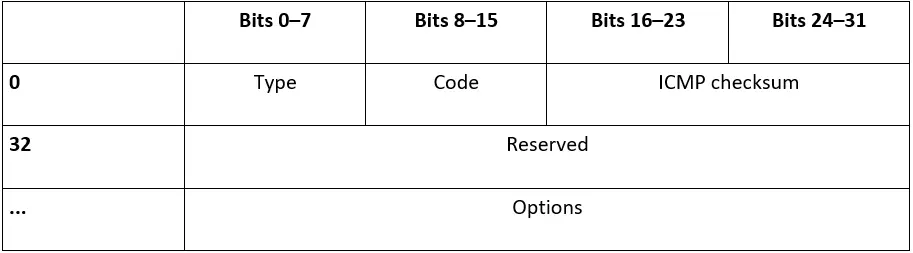
Router solicitations are messages that a host can send to request all routers on the network to send advertisements to the addressed router. These then respond with a type 134 message, either exclusively to the requesting host (unicast) or to all network subscribers (multicast). With this message type, such as a network connection, a host does not need to wait for the network router to automatically notify itself. This type of ICMPv6 message is structured as follows:
The default configuration of an NDP-ICMPv6 type 133 message thus provides a minimum length of 64 bits. ‘Type’ is assigned the router solicitation value 133, while ‘Code’ is set to 0 again. The two other mandatory fields are the ICMP checksum (16 bits) and a 32-bit long ‘Reserved” field, which remains unused.
The only possible option that can be attached to the message is the MAC address of the sender.
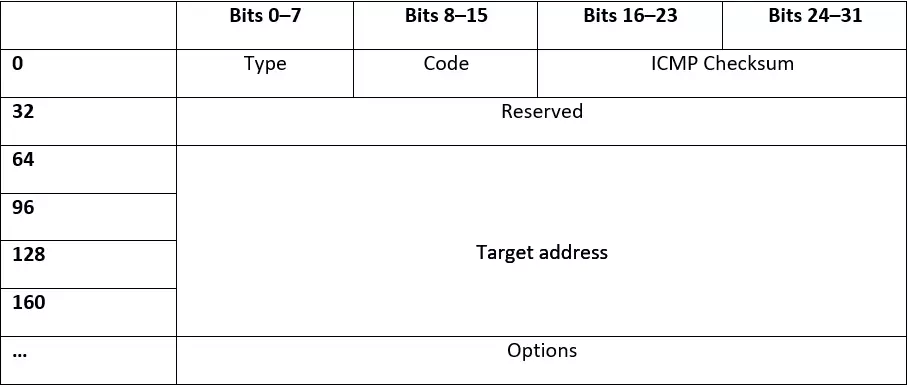
Type 135: Neighbor Solicitation
Network clients send neighbor solicitations to discover the MAC address of the target host, and in return, optionally provide their own address. ICMPv6 messages of this type can either transmit devices via multicast if they want to determine an address, or via unicast if they are only checking whether a neighbor is present.
Like all ICMPv6 message types, neighbor solicitations starts with 8-bit type identification – in this case, ‘type’ has the value 135. This is followed by the 8-bit long code, which is set to 0, and the 16-bit checksum. The ‘Reserved’ field remains unused, as with the previously presented messages.
With 128 bits, the targeted IP address which cannot be a multicast address, makes the bulk of the message, with a total length of at least 192 bits. This type of message, which is decisive for the Neighbor Discovery Protocol, also allows the MAC address of the sender as an optional additional specification.
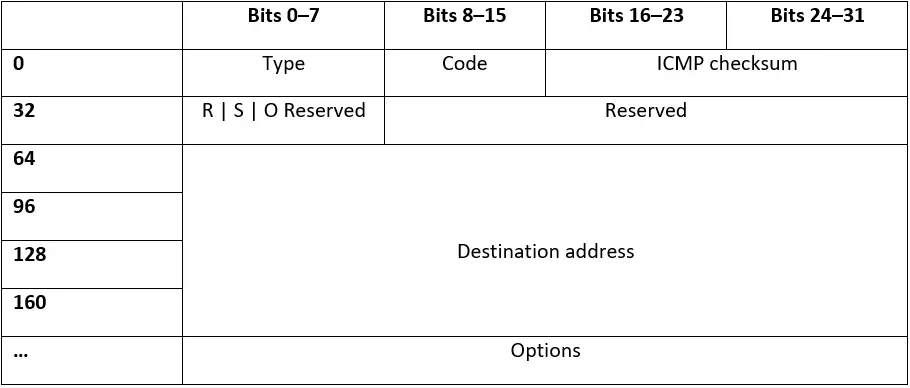
Type 136: Neighbor Advertisement
On the one hand, network devices send neighbor advertisements in response to requesting neighbor solicitations, but on the other hand, also send unsolicited messages to inform other participants about changes in the address configuration. The structure of these kind of messages are as follows:
The first 32 bits of the standard 192-bit neighbor advertisement are based on the typical ICMPv6 message scheme: ‘Type’ (136) and ‘code’ (0) are reserved for 8 bits, followed by the 16-bit checksum. Three individual bits continue the message code, for which the following conditions apply:
- R: The ‘R’ bit is sent when the message is sent from a router.
- S: If the message contains the ‘S’ bit, it is a response to a unicast neighbor solicitation, which confirms that the network user is reachable. This bit cannot be set in response to multicast requests, or in specifically initiated neighbor advertisements.
- O: The ‘O’ flag instructs the recipient of the message to override the existing cache entry.
The subsequent 29 bits are reserved according to the known pattern, so they remain unused, and are initialized with 0 and ignored by the receiver. The 128-bit destination address is now followed by the main part of the message: either the IP address from which the neighbor advertisement has been requested, or the address for which a new MAC address will be posted. The router also has the option to name its own address – mandatory when responding to a multicast request.
Type 137: Redirect
Routers have the ability to inform network hosts about a better first hop on their way to specific destination addresses. To do so, they send NDP-ICMPv6 redirects, which are characterized by the following scheme:
With a minimum length of 320 bits, redirects are the largest ICMPv6 messages that are relevant to how the Neighbor Discovery Protocol functions. The typical structure with bit strings for the type identification (137), the code (0), the checksum and an unused “reserved” field (32 bits) are followed by the address of the recommended hops and then the address for which both of these redirections are recommended (both 128 bits). Optionally, the message packet may include the destination’s MAC address, as well as the header of the redirected packet.
NDP tasks and possibilities at a glance.
There is a lot to the caching mechanisms and communications of the Neighbor Discovery Protocol in conjunction with the Internet Control Message Protocol. The following NDP scenarios illustrate the interplay and functionality of the two protocols:
- Detecting the router and network prefix: All routers in a network routinely broadcast router advertisements via multicast to all network operators. These include, among other things, information like the address, network prefix and routing used to create the default router list, as well as the prefix list. These clients are then used to determine the default gateway and subnet mask. Since all entries have only a limited validity period, only active routers remain. The router advertisements can also be enforced using router solicitations.
- Determining important parameters for packet transmission: Router advertisements can also optionally contain information about which parameter the participating clients have to apply when delivering packets. This can be very specific information, such as the maximum packet size, but also broad internet parameters, such as the fixed limit of intermediate stations for outgoing packets.
- Identifying the next hop: If a packet is being sent, the NDP protocol ensures that the destination cache already contains a corresponding entry for the targeted destination host. If this is not the case, the protocol determines the next intermediate station using the information from the prefix list and the default router list. Subsequently, the new state of knowledge is stored in the destination cache, which is immediately available when a new request is made. If the newly created entry does not already have an equivalent in the neighbor cache, this is automatically generated and then the address resolution is initiated.
- Resolving the IP address in the MAC address: In order to determine the MAC address of a specific host in the network, it receives a neighbor solicitation via IPv6 multicast to its own specific multicast address. Only the host can respond to this unique address combination. It sends a neighbor advertisement in response with the MAC address stored by the output client in the neighbor cache. The Neighbor Discovery Protocol is thus used to identify neighbors, as well as to determine routers.
- Detecting negligence of a neighbor: All MAC addresses stored in the neighbor cache must be regularly checked for their relevance. As long as TCP/IP data or receipts are sent from a registered address, this is logically considered to be active and the host hiding behind it can be reached. If there has not been a data exchange with the relevant device for a long time, and the entry’s validity period has expired, this is marked as outdated. To check whether the respective host is no longer accessible, an ordinary data packet is sent to the registered address first. If an answer returns, one final test is started via Unicast neighbor solicitation. If this confirms non-availability, the entry from the neighbor cache disappears.
- Detecting duplicate addresses: If a device has auto-configured an address, NDP classifies it as ‘tentative’ (temporary). For this purpose, the newly connected network client sends a neighbor solicitation to the temporary address that he wants to use himself – with a temporarily unspecific sender address. If another host is already using the address, they respond with a neighbor advertisement message to the general multicast address. The checking client also receives this message, which suggests a new address.
- Informing about redirect options: The Neighbor Discovery Protocol gives routers with the redirect message the ability to optimize the path from data packets to the targeted hosts. As noted above, they can use ICMPv6 type 137 to make recommendations for more appropriate intermediate stations that are included in the destination cache.
How to inspect the neighbor cache on your system
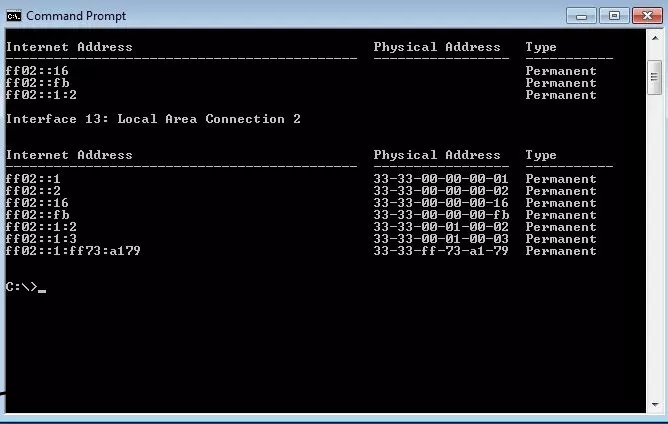
Whether Windows, MacOS, Linux, iOS or Android – modern operating systems support IPv6 and are able to access the possibilities of NDP in ethernet-based networks. By using the appropriate instruction, you can use the command line at any time to call the neighbor cache that was created for your device.
In Windows for example, you can list your network neighbors using the netsh (network shell) program and the following command:
netsh interface ipv6 show neighborsWith most Linux distributions, you can access the neighbor cache using the iproute2 tool and this command:
ip -6 neighWith macOS and other BSD-based distributions, access the cache entries as follows:
ndp -a