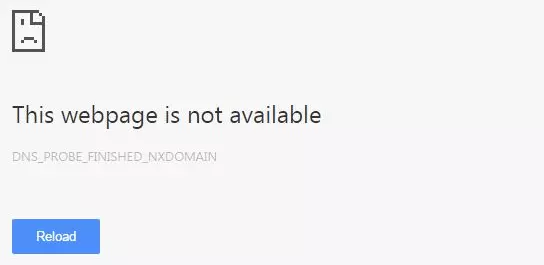
How do you fix DNS_PROBE_FINISHED_NXDOMAIN?
When your browser displays an error message instead of loading the website you want, finding clear and reliable advice can be difficult. In Chrome, the “DNS_PROBE_FINISHED_NXDOMAIN” notice means the domain name couldn’t be translated into its corresponding IP address. In this…