SP-PhotoShutterstock
SP-PhotoShutterstockWhat is port scanning?
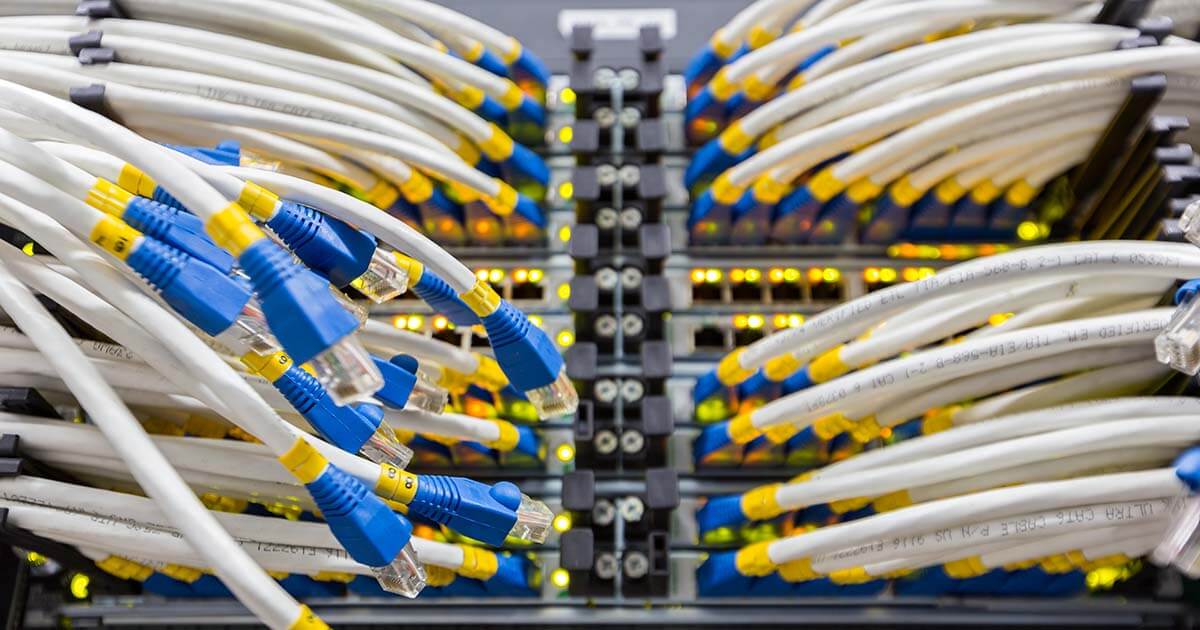
It’s easy to lose track of all the different programs that are responsible for inbound and outbound data traffic. Networks hosting a large number of computer systems that are constantly communicating with online services often require technical backup. High-performance tools…